DEDICATED SUPPORT
All users can watch the crypter tutorials and how to bypass videos. We will support all Private users vie TeamViewer, Email, Telegram Chat. Use best FUD Crypter.
PRIVATE STUB with 100% GUARENTEE
We would recommend that you purchase the The private package, with guaranteed to bypass Windows Defender if the FUD results are essential to you.
SHARED STUB
You can buy fud Crypter shared package. The shared package depends on other users’ behavior. So other users can’t get clean results if anyone uploads the payload on website that distribute the samples. So anyone who uses it faster can get FUD results.
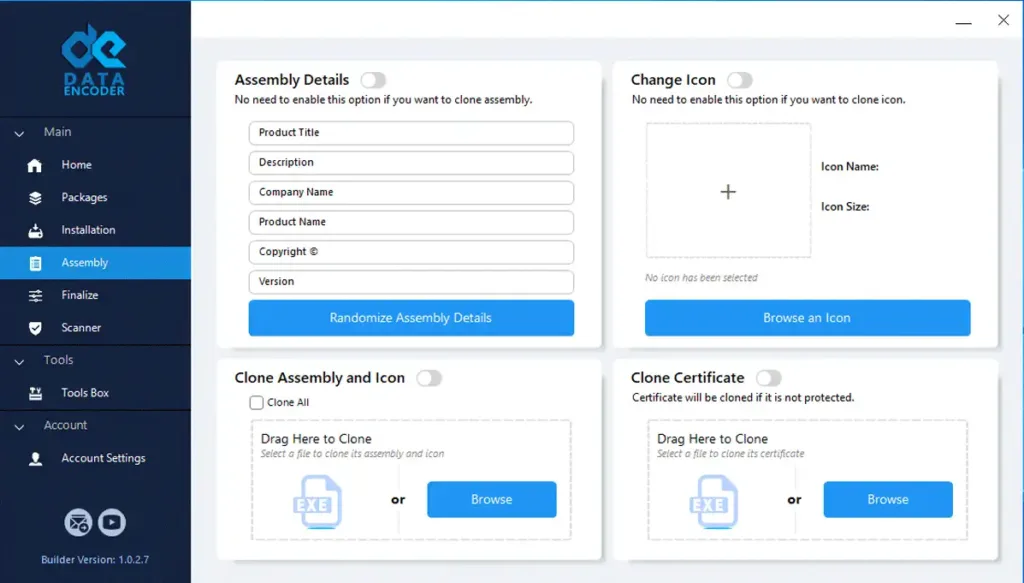
MANAGE ASSEMBLY or CERTIFICATE
Data Encoder give various options to change the payload’s assembly or clone Certificate or clone assembly from a file.
UNLIMITED CRYPTS
You can encrypt payloads unlimitedly in each any Data Encoder packages. Malware packers have a problem with this.
RUNTIME CHECKER & SCANNER
You can test your encrypted payload with inbuilt scanner for Scantime results. Also, check your Runtime payload status upload your file to Runtime checker tool.
Download Free FUD Crypter
Data Encoder Crypter hasn’t any free version.
Download Crypter From GitHub
Be careful of fraudsters, especially do not download any files in our name on GitHub.
Download Free Crypter
Note any free Crypter can’t give you FUD results especially on Runtime. Most of the are infected.
Choosing the right FUD Crypter for your needs
FUD Crypter, short for “Fully Undetectable Crypter,” is a powerful tool designed to protect your software from detection. It works by encrypting and modifying the binary code of your software, creating a completely new file that appears harmless to antivirus scanners and malware analysts. When selecting a FUD Crypter, it’s important to consider your specific needs and requirements. Here are a few factors to keep in mind when making your decision:
1. Compatibility: Ensure that the FUD Crypter you choose is compatible with your software and operating system. Compatibility issues can lead to unexpected results or even failure to protect your payload effectively.
2. Encryption strength: Different FUD Crypters offer varying encryption options. Consider the sensitivity of your software and choose a Crypter that provides the appropriate level of protection.
3. Ease of use: Look for a FUD Crypter that offers a user-friendly interface and straightforward operation. This will make it easier for you to integrate the Crypter into your software development process.
4. Support and updates: Check if the FUD Crypter you’re considering offers regular updates and technical support. This ensures that you have access to the latest security measures and assistance when needed.
FUD Crypter Pricing Plans
We Have Pricing Plans To Suit Everybody Need. Choose between the shared STUB and Private STUB
Windows Defender is a critical component of Windows security, but advanced malware and best crypter present formidable challenges to its detection capabilities. We recommend buy FUD crypter and don’t use the free ones. The free Crypter can’t bypass antivirus on Runtime.
Data Encoder serve as powerful tools employing advanced encryption techniques to encrypt Payload , rendering them undetectable by antivirus software.
The sophisticated techniques employed by top crypter, such as DLL injection, code obfuscation, and evasion tactics, often make it difficult for Windows Defender to identify and thwart these threats. Therefore the best Crypter help to bypass Windows Defender. For bypass Microsoft SmartScreen follow our guide.
Do you get Chrome warning? It isn’t related to crypter. just follow the guide. Also, We recommend watching bypass antivirus videos for more details.